Evil Corp Cybercrime Ring Shut Down by UK and Allies
Sixteen members of the notorious Evil Corp, once dubbed the world’s biggest cybercrime threat, have been hit with fresh UK sanctions. The crackdown exposes their ties to the Russian state and infamous ransomware gangs like LockBit. This comes as part of a joint operation with Australia and the US, the latter unveiling an indictment against a key Evil Corp player.
From Moscow Mob to $300 Million Cybercrime Syndicate
The National Crime Agency (NCA) spearheaded a massive probe tracking Evil Corp’s rise from a small-time Moscow crime family to a global cyber syndicate raking in over $300 million. Victims ranged from hospitals to government bodies and critical infrastructure worldwide.
Back in 2019, the NCA’s work helped nail Evil Corp’s leader Maksim Yakubets and admin Igor Turashev with US indictments and sanctions. Now, the UK Foreign Office has slapped sanctions on them again, plus seven others already targeted in the US—and seven fresh faces previously unknown.
Key Figures Exposed: Russian Intel Links Revealed
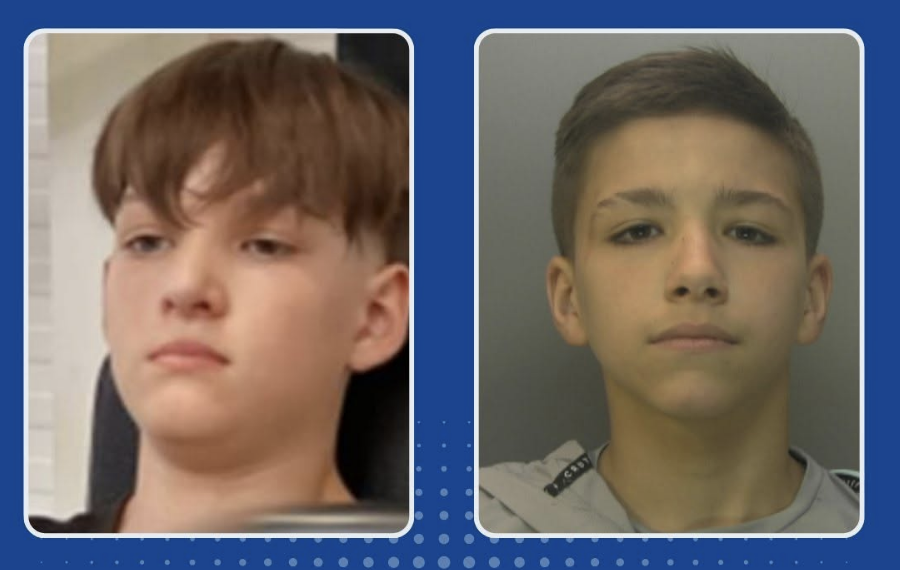
- Aleksandr Ryzhenkov, Yakubets’ right-hand man and mastermind behind some of Evil Corp’s most vicious ransomware, has been sanctioned. He’s also linked to LockBit and faces US charges for BitPaymer ransomware attacks on American victims.
- Viktor Yakubets, Maksim’s father, and Eduard Benderskiy, his father-in-law and ex-high-ranking FSB official, were sanctioned. Benderskiy helped shape Evil Corp’s ties to Russian intelligence, facilitating cyberattacks against NATO allies before the group’s first sanctions in 2019.
The Rise and Fall of Evil Corp
Formed in 2014, Evil Corp targeted banks in over 40 countries, stealing over $100 million with ransomware like BitPaymer and Dridex. Shielded by Russian state connections, they operated brazenly—until 2019’s US sanctions and indictments shook them hard.
Their operations stalled, forcing the gang underground to reinvent tactics and develop fresh ransomware strains like WastedLocker, PhoenixLocker, and PayloadBIN. Some members, like Ryzhenkov, switched to using ransomware from other groups such as LockBit.
Global Efforts Keep Up the Pressure
The NCA continues to monitor Evil Corp’s shadowy remnants and LockBit affiliates, with recent arrests in the UK, France, and Spain linked to ransomware infrastructure and attacks. Operation Cronos, led by the NCA, remains active against these cybercriminal networks.
Government Officials Sound the Alarm
James Babbage, NCA Director General, said: “These sanctions expose further Evil Corp members, including LockBit affiliates critical to their criminal activities. We expect these designations to disrupt their ongoing operations.”
Foreign Secretary David Lammy added: “I am making it my personal mission to wield the full arsenal of sanctions against the Kremlin. This sends a clear message – Russian cyberattacks will not be tolerated.”
Security Minister Dan Jarvis said: “Cybercrime causes huge harm worldwide, but yesterday’s action proves there are serious consequences for those involved.”
Jonathon Ellison from the NCSC warned: “Ransomware hits UK victims hard, disrupting vital services and risking data. These sanctions show we’re united with allies to stop cybercrime dead in its tracks.”
Defend Yourself Against Ransomware
The NCSC urges organisations to follow its ransomware guidance and have solid response plans in place. This coordinated UK-US-Australia crackdown highlights a relentless effort to punish cybercriminals and make their illicit profits impossible.
One thing’s clear: no cyber crook, no matter how slick or well-connected, is safe from the long arm of justice.